Product Cybersecurity Policy
Support Scope and Product Lifecycle
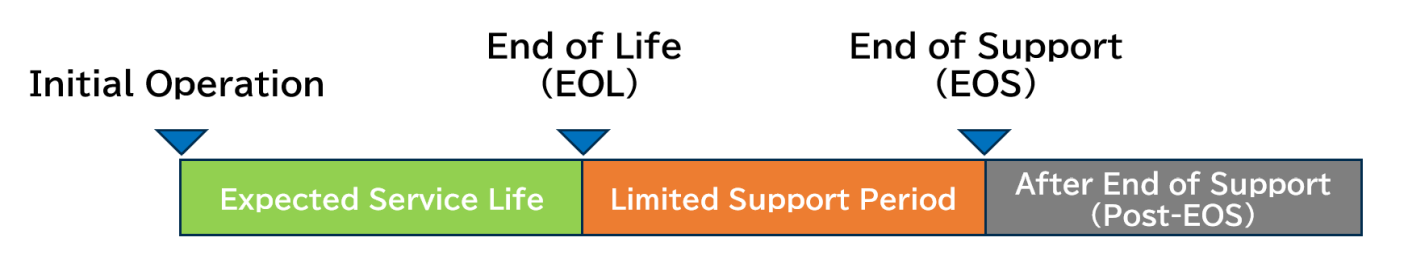
EOL/EOS Policy
EOL (End of Life)
The end of the expected service life defined by our company for each product, assuming that appropriate daily inspections, maintenance inspections, and preventive maintenance are performed from the time of initial operation, allowing the product to maintain its effectiveness and safety.
EOS (End of Support)
The period from the initial operation until the end of support date defined by our company for each product.
Basic Policy
We implement appropriate measures against cybersecurity threats throughout the entire lifecycle of the devices that we manufacture and sell. In accordance with the following policies, we will take action in response to the End of Life (EOL) and End of Support (EOS) of our products. In addition, for products manufactured by third parties and procured and sold by our company (resale products), cybersecurity measures are handled within the responsibility of the original manufacturer or rights holder.
Support Phases and Scope of Services
[ Phase I ]
Support Period (until EOL)
1. Vulnerability Monitoring and Response
We will monitor vulnerabilities in the product, implement necessary fixes, and provide security-related software updates and vulnerability patches.
2. Security Updates
For security vulnerability responses of software developed by our company, we will provide security updates when deemed necessary based on vulnerability severity, risk analysis, and other factors.
For software outside the scope of our development, we will provide updates when security updates are prepared by the supplier.
3. OS Updates
When deemed necessary in conjunction with updates to software developed by our company, we will provide corresponding OS updates.
Where customers provide the software operating environment, customers may be required to update the OS as their own responsibility to maintain security and ensure stable product operation.
[ Phase II ]
Limited Support Period (from EOL to EOS)
1. Vulnerability Monitoring and Response
We continuously monitor vulnerabilities associated with the product, and when, based on risk analysis, we determine that action is necessary, we will implement corrective measures—such as configuration changes or the provision of patches—to the extent feasible.
2. Security Updates (Conditional)
Security updates will be provided only when all of the following conditions are met:
- The software was developed by our company or under our scope of responsibility;
- An update has been provided by the software supplier;
- The hardware specifications satisfy the update requirements;
- Implementation is technically feasible.
3. OS Updates Supports(Limited)
For operating systems outside our development scope, such as Windows® or embedded OSs, we generally do not provide OS updates.
However, if we determine that countermeasures are necessary in response to a critical security threat, we will consider implementing such measures only when all of the following conditions are met:
- The hardware specifications satisfy the requirements for the OS update;
- Implementation is technically feasible.
[ Phase III ]
After End of Support (Post-EOS)
Support for products that have reached End of Support (EOS) will be discontinued, and the supply of consumables may also be terminated.
As a general rule, we do not provide any security measures, including vulnerability fixes; therefore, we recommend planning for the replacement of such equipment. Furthermore, if you choose to continue using the product after the EOS period, you will be responsible for implementing appropriate cybersecurity measures.
Important Notice
- This policy is intended to ensure the safety of medical devices and reduce cybersecurity risks.
- Feasibility of responses will be determined on a case-by-case basis depending on product specifications, technical constraints, and the nature of the threat.
- If you continue to use products after EOS, please strengthen your own security measures.





































 TOP
TOP